What Is EXIF Data and Why You Should Remove It Before Sharing
EXIF metadata in your photos reveals GPS location, device model, and timestamps. Learn what it is, why it matters, and how to strip it before sharing.

Every photo you take on a phone carries more than pixels. Embedded inside the file is a block of data called EXIF — and it can tell a stranger exactly where you were, what device you used, and when the shot was taken.
Most people never see it. Most people never remove it. That is the problem.
What EXIF data actually contains
EXIF stands for Exchangeable Image File Format. It is a standard that cameras and phones use to store technical and contextual information alongside the image itself.
Here is what a typical iPhone photo contains:
| Field | Example value | Risk |
|---|---|---|
| GPS Latitude | 31.230416° | Reveals your exact location |
| GPS Longitude | 121.473701° | Down to a few meters |
| Device Model | iPhone 15 Pro Max | Device fingerprint |
| Lens | 6.86mm f/1.78 | Narrows device identity |
| Serial Number | C39V… | Unique hardware ID |
| Date Taken | 2026-04-05 14:32:07 | Timestamps your activity |
| Software | iOS 18.3.2 | OS version fingerprint |
| Exposure | 1/120s, f/1.78, ISO 64 | Not sensitive, but included |
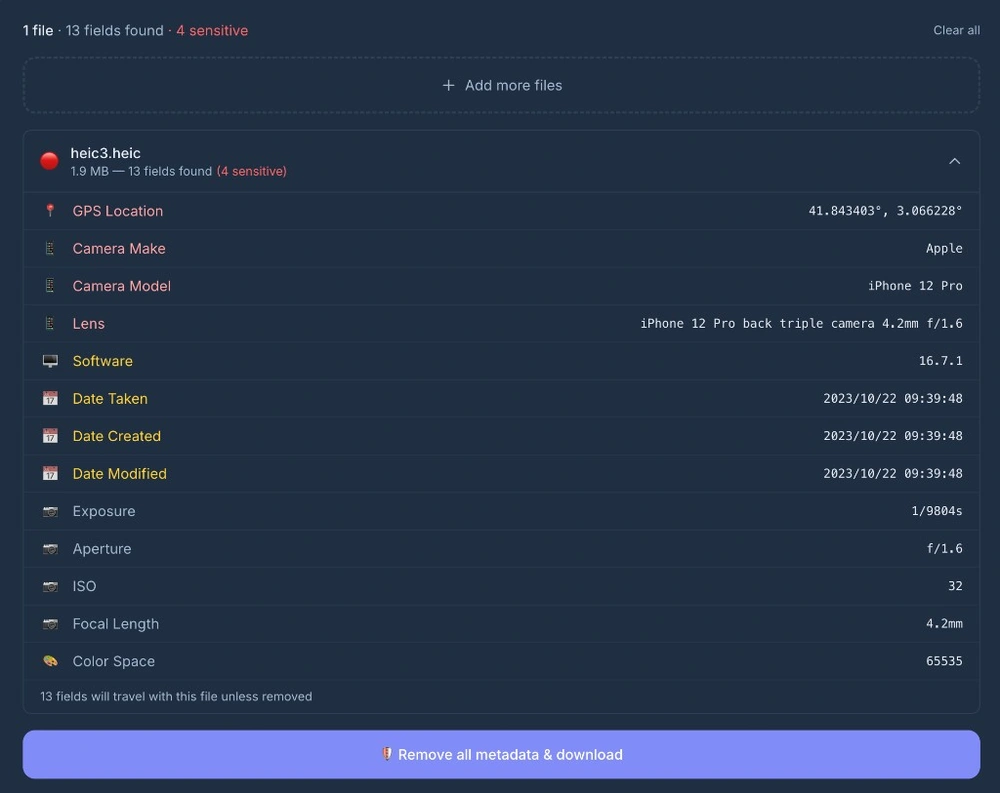
Here is what that looks like in practice — a single iPhone photo scanned by PicShift’s metadata remover, revealing 13 embedded fields including GPS coordinates:
That GPS coordinate? Paste it into Google Maps and you get a pin on the building where the photo was taken. If that building is your home, your office, or your child’s school — you have a problem.
Why most people do not know about it
People search “what is metadata in a photo” and expect something complicated. It is not. EXIF is just invisible. You open a photo, you see an image. The metadata sits in a separate block inside the file binary. No photo viewer shows it by default.
Even tech-savvy people forget about it. You crop a photo, apply a filter, export it — and the EXIF data survives all of that unless you explicitly strip it.
Real cases where EXIF data caused harm
This is not a theoretical risk. It has happened repeatedly:
- John McAfee located and arrested (2012). The cybersecurity pioneer was hiding in Guatemala. He posted a photo to his blog, and the embedded GPS coordinates pinpointed his exact location. Authorities arrested him within hours.
- Anonymous hacker caught through girlfriend’s photo (2012). Higinio Ochoa of the hacktivist group CabinCr3w posted photos taken on an iPhone to taunt law enforcement. GPS coordinates in the EXIF data led investigators straight to his house in Galveston, Texas.
- McKayla Maroney’s home address exposed (2014). A hacker extracted GPS coordinates from leaked photos of the Olympic gymnast, used Google Maps to identify her home, and posted the address alongside realtor listings.
- Instagram influencer forced to relocate. An influencer with 500K followers had her home address discovered when followers extracted GPS data from her workout photos. Stalkers showed up at her house.
These are not edge cases. They are what happens when EXIF data meets someone motivated enough to look.
When EXIF data becomes a problem for you
Not every photo needs cleaning. A landscape you shot in a public park? Probably fine. But here are cases where leaving EXIF in is a genuine risk:
- Photos of your home or workplace. GPS pins your address. If you list something for sale online and include a photo taken at home, the buyer knows where you live.
- Photos of children. Location + timestamp + school building = pattern that should not be public.
- Screenshots with software tags. Photoshop version, Lightroom build number, even operating system version can be useful for targeted attacks.
- Images sent to strangers. Freelance work, marketplace listings, dating apps — you do not want a stranger to know your GPS trail.
- Batch uploads to public platforms. Not all platforms strip EXIF consistently. Relying on Instagram or WhatsApp to clean your metadata is a gamble.
What platforms actually strip and what they keep
This is the part that surprises people. The answer is “it depends, and it changes.”
| Platform | Strips GPS? | Strips device info? | Notes |
|---|---|---|---|
| Yes | Mostly | Strips on upload | |
| Yes | Yes | Strips everything | |
| Yes | Mostly | Strips on upload | |
| Discord | Yes (now) | Yes (now) | Changed in 2023 — used to keep everything |
| Telegram (as photo) | Yes | Yes | Only when sent as compressed photo |
| Telegram (as file) | No | No | ”Send as file” preserves all EXIF — big catch |
| Slack | GPS only | No | Strips GPS since 2020, keeps device model |
| Email attachment | No | No | Full EXIF intact |
The tricky one is Telegram. Most people use “Send as file” to preserve image quality without realizing it also preserves their GPS coordinates. Discord used to be a major risk but started stripping EXIF in 2023 — if you search older articles, you will find outdated advice saying Discord keeps everything.
The safest approach: remove metadata yourself before sharing. Platform policies change, and the one time you assume a platform strips EXIF is the time it does not. For a full breakdown, see which platforms strip EXIF and which don’t.
How to remove EXIF metadata
Three common approaches, from least to most practical:
1. Command-line tools (exiftool)
exiftool -all= photo.jpgFast and thorough, but requires terminal comfort. Not realistic for most people.
2. Desktop apps (ImageOptim, GIMP, Preview)
Some image editors have a “remove metadata” option in export settings. Works, but requires opening each file individually.
3. Browser-based tools
Drop images into a web tool, get cleaned files back. The catch: most “free EXIF removers” upload your photo to their server first — which means they see your metadata before you can remove it.
PicShift’s metadata cleaner works differently. It runs entirely in your browser using WebAssembly — a local EXIF remover with no server upload. Your images never leave your device. You can verify this by turning off Wi-Fi — the tool still works.
What stays after removal
After stripping EXIF, the file contains only pixel data. No GPS, no device info, no timestamps, no software tags.
The image looks identical. File size may change slightly (a few KB smaller, since the metadata block is gone). Visual quality is unaffected.
One thing to be clear about: removing EXIF does not anonymize the image content itself. If the photo shows a recognizable building or street sign, that information is still visible. EXIF removal protects against hidden metadata, not visible content.
Why you should care
EXIF metadata is useful for photographers who want to track their settings. It is a privacy risk for everyone else sharing photos online.
The fix takes seconds. Check what is inside your photos, strip what you do not want to share, and download the clean version. That is it.
Remove EXIF data from your photos →
If you want to understand exactly what PicShift does and does not see, our privacy and local processing guide walks through the architecture: every conversion happens inside your browser, source images are never uploaded, and the small amount of traffic data we do receive is documented in plain English.